Identity Deepfake Threats to Biometric Authentication Systems
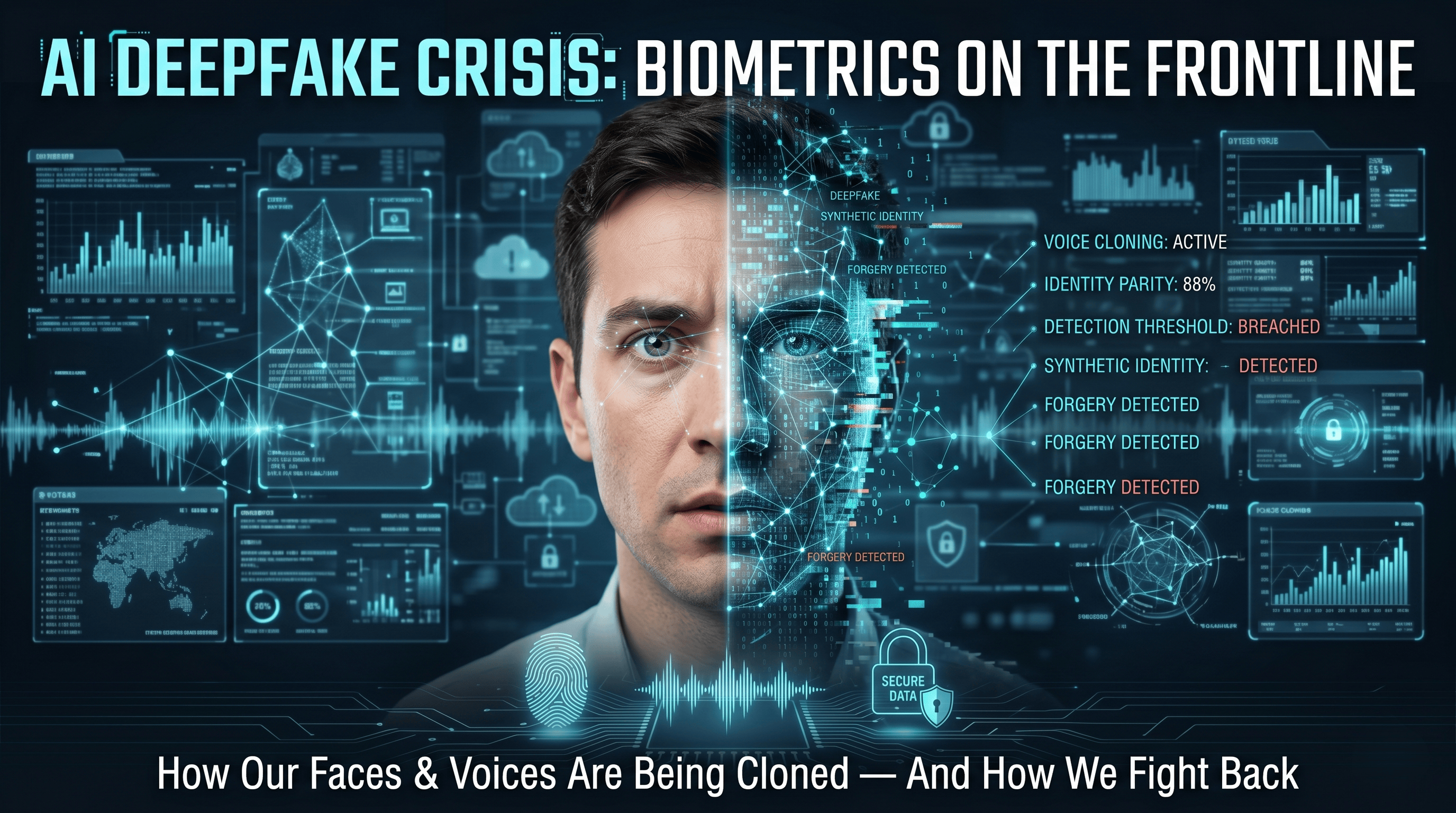
We unlock our phones with a glance and access our bank accounts with a fingerprint without a second thought. This seamlessness has bred a kind of "outsourced trust"—a widespread assumption that if banks and governments rely on biometrics, the technology must be foolproof.
Generative AI, however, is turning that assumption on its head. A recent paper, "Identity Deepfake Threats to Biometric Authentication Systems: Public and Expert Perspectives", highlights a growing reality: the biometric systems we rely on every day are increasingly vulnerable to deepfakes.
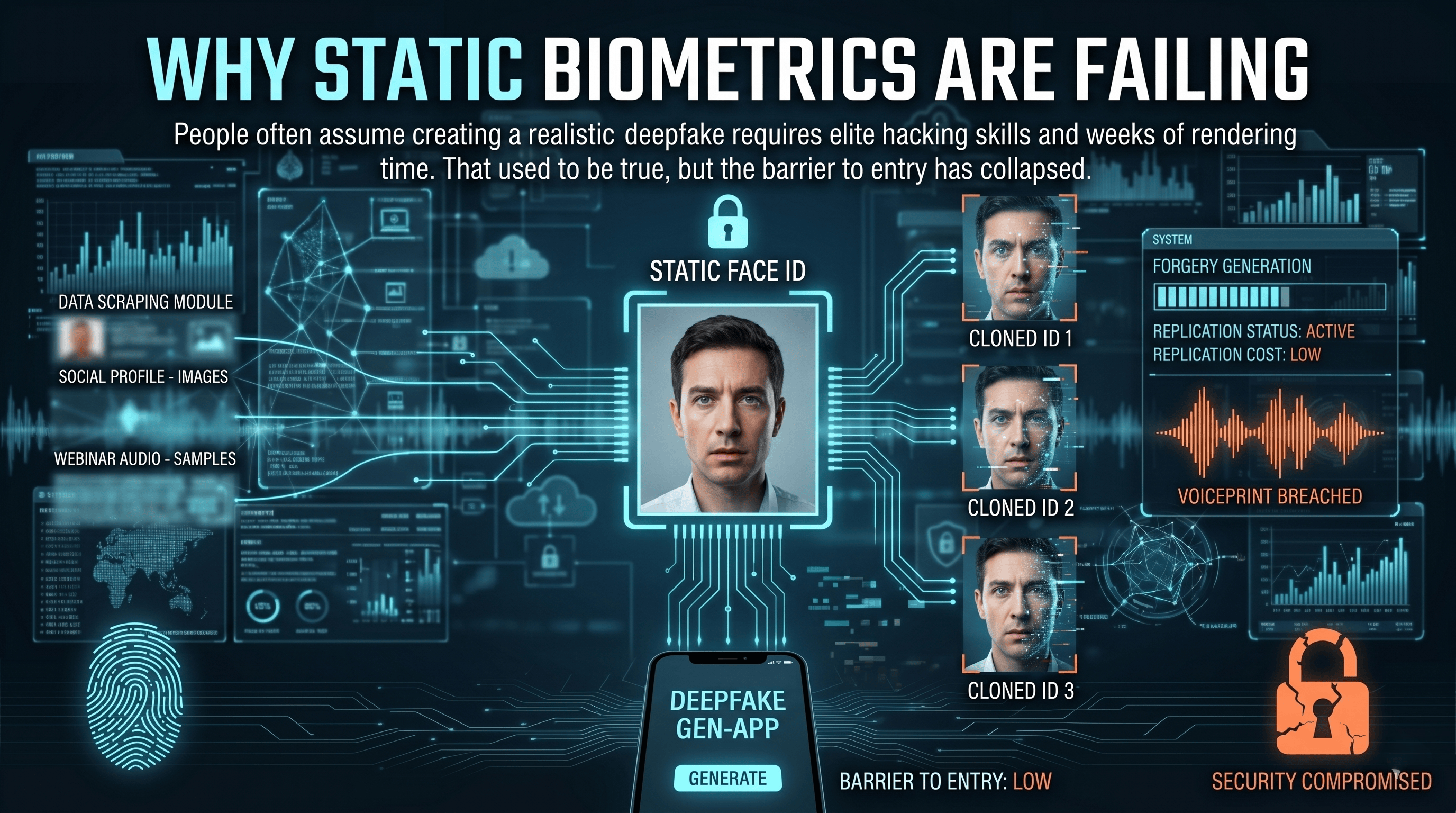
Why Static Biometrics Are Failing
People often assume creating a realistic deepfake requires elite hacking skills and weeks of rendering time. That used to be true, but the barrier to entry has collapsed. Anyone with a smartphone and cheap cloud access can now generate high-quality deepfakes in a matter of minutes.
The raw material for these forgeries is already out there, too. Attackers can easily scrape audio and video snippets from our social media profiles or public webinars to train sophisticated generative models. Because of this, traditional, static biometric markers—like a clear photo of your face or a standard voiceprint—are no longer secure. They are easily stolen, easily copied, and easily weaponized against the systems designed to protect us.
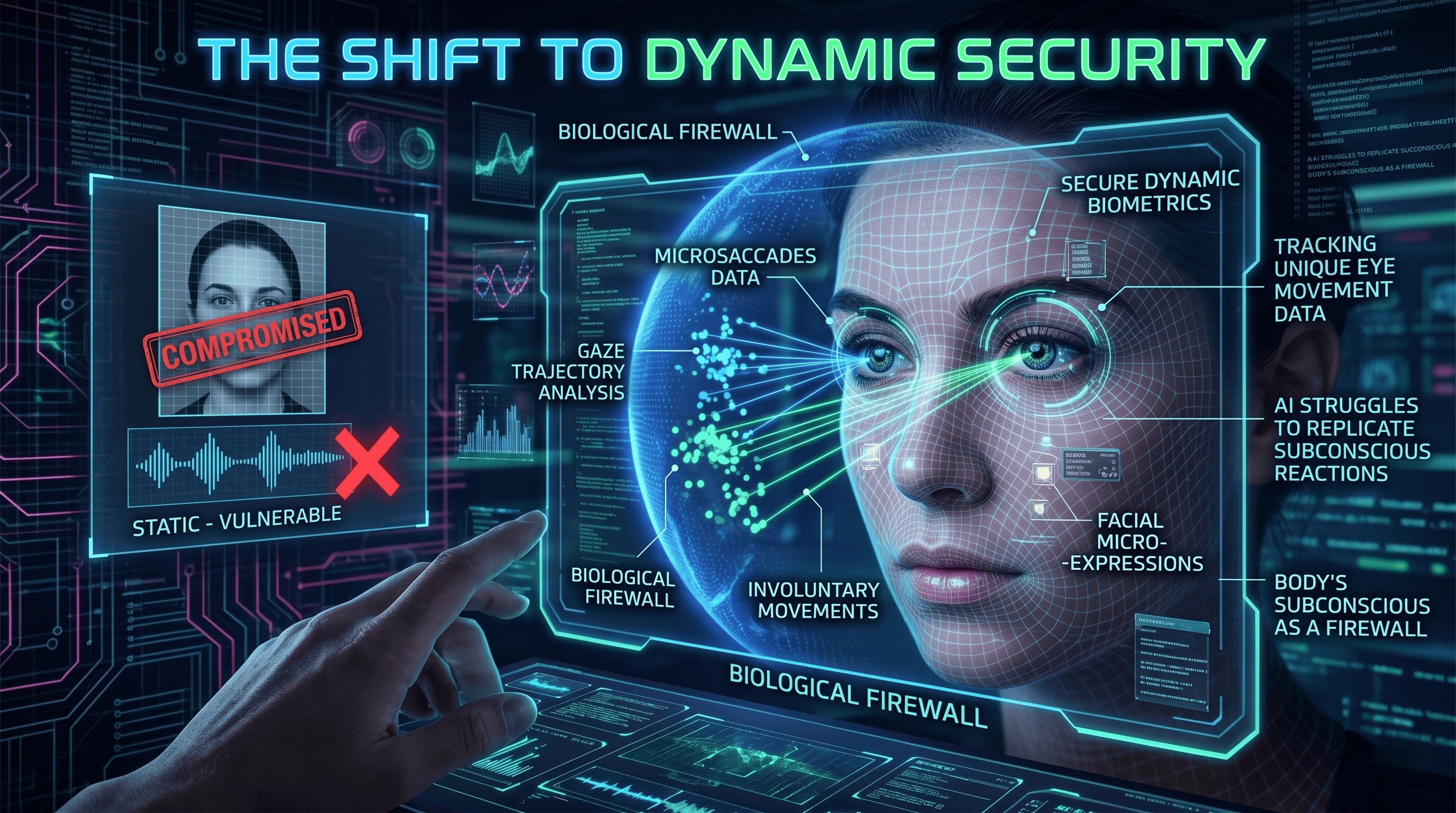
The Shift to Dynamic Security
If static faces and voices are compromised, researchers suggest moving away from static recognition entirely. The new focus is on "dynamic and involuntary" biometric signals.
While AI is excellent at mimicking what you look like, it struggles to replicate how your body subconsciously reacts. This includes involuntary micro-movements, like microsaccades (tiny eye movements), gaze trajectories, or fleeting facial micro-expressions. Because these continuous data patterns are outside our conscious control, they act as a biological firewall that current generative AI models find incredibly difficult and computationally expensive to replicate. In the near future, logging in might not just involve a camera checking your face, but rather tracking the unique way your eyes move across the screen.
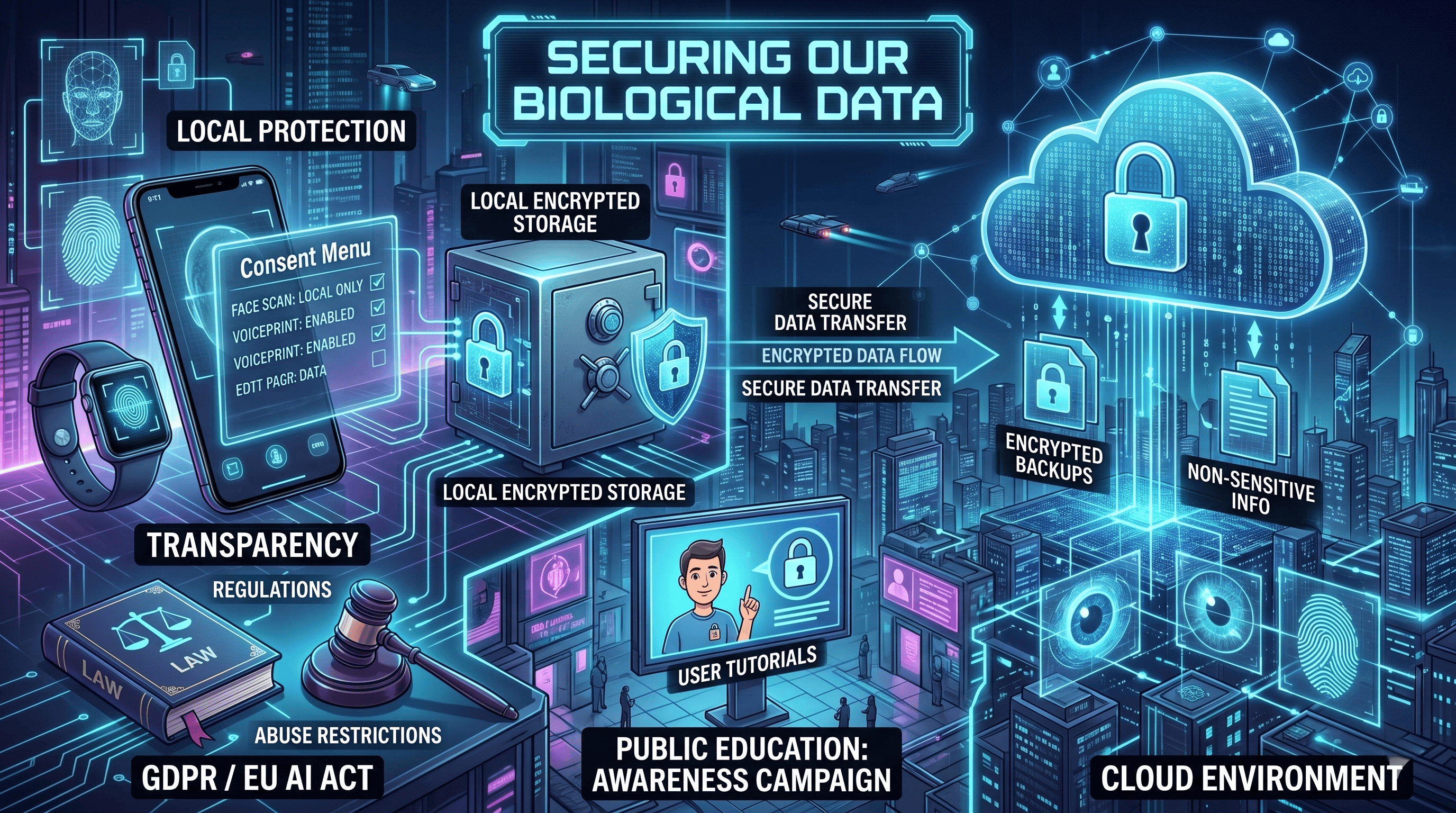
Securing Our Biological Data
Upgrading the technology is only half the battle; the other half is deciding how this highly sensitive data is stored and managed. Security experts recommend a hybrid storage model: your most sensitive biometric data stays locked locally on your device, while the cloud only handles strictly encrypted backups or non-sensitive information.
Furthermore, transparency is critical. App developers need to ditch the dense legal jargon and offer clear, straightforward consent menus so users actually understand what they are agreeing to. On a broader scale, policymakers need to step in with robust regulations—similar to the GDPR or the EU AI Act—to penalize inadequate data protection and restrict technological misuse. Parallel to this, public education campaigns are essential to get everyday users up to speed on basic biometric security risks.
Looking Ahead
The arms race between deepfakes and biometric security is already underway. As authentication systems evolve to counter these threats, we’ll likely see a shift toward more complex verifications—like eye-tracking scans—which might take a fraction of a second longer than a standard face unlock. Understanding why these changes are happening, and demanding better privacy standards for the data that powers them, is our best defense against biometric fraud.